A documentation update published on May 11, 2026 to Google's Tag Platform developer site has formalized a capability that analytics engineers spotted this week: the Google tag gateway for advertisers now supports concealing Google Tag Manager container IDs behind randomized alphanumeric serving paths. The change extends the existing first-party serving architecture with an obfuscation layer that makes it harder for ad blockers to identify and suppress GTM scripts based on known container ID patterns.
The feature is part of the broader Google tag gateway for advertisers infrastructure, which Google brought to general availability on May 8, 2025 with Cloudflare as the launch CDN partner and an 11% uplift in observed signals as the headline metric.
What the documentation update specifies
According to Google's updated developer documentation, the tag gateway for advertisers lets operators load Google scripts - including gtm.js and gtag.js - directly from their own first-party infrastructure rather than from Google's servers. The documentation covers two primary deployment paths: through a tagging server or through a CDN. The tagging server option, which is the focus of the container ID cloaking capability, requires a server container already configured in Google Tag Manager, a running tagging server, and a custom server domain.
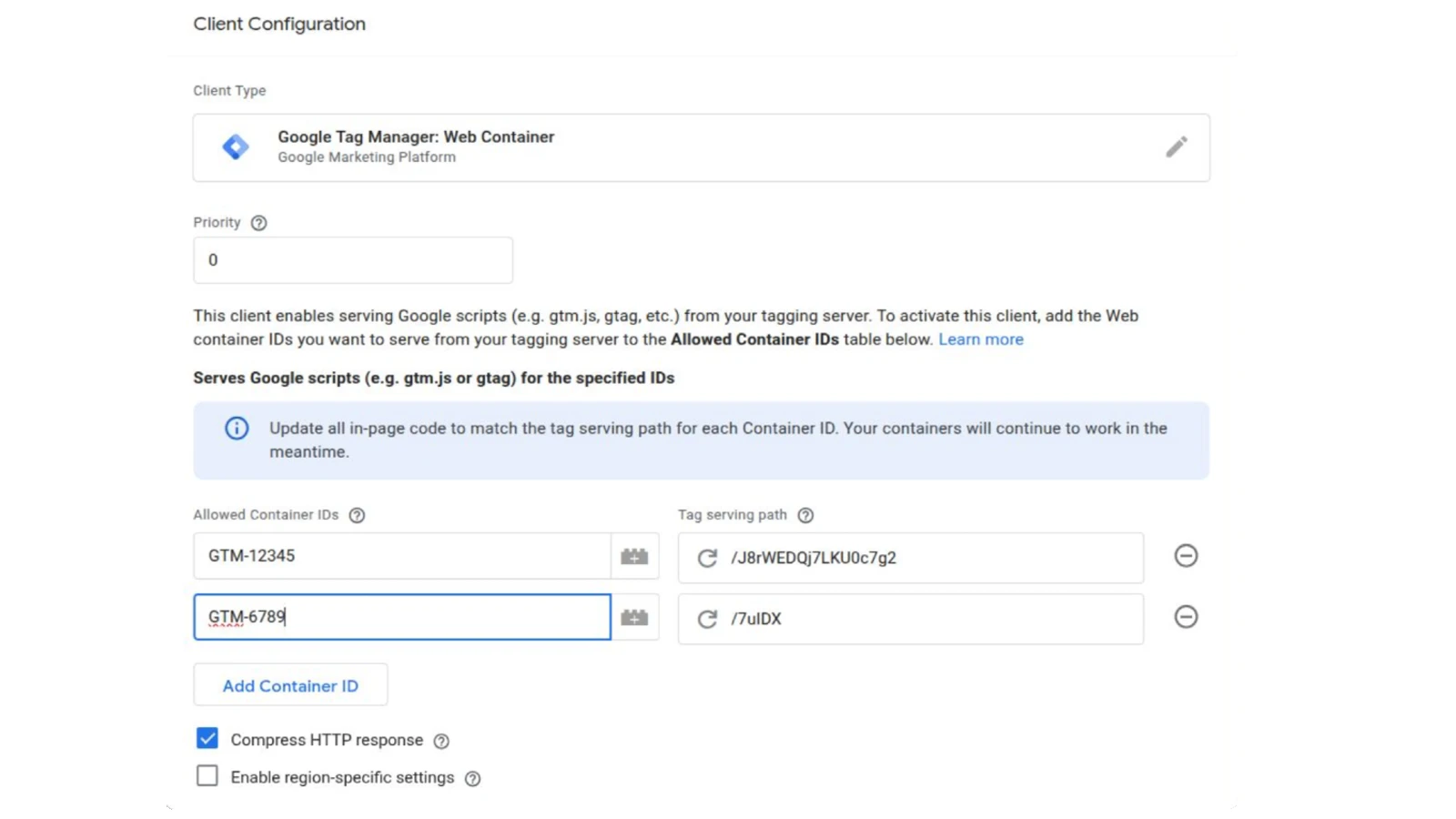
The core of the obfuscation mechanism lies in how the Web Container client type is configured inside the server container. When a new container ID is added to the "Allowed Container IDs" field in the client configuration, GTM automatically generates a tag serving path made of random alphanumeric characters. According to the documentation, "when a new container ID is added, a path made of random alphanumeric characters is automatically generated to help prevent conflicts with existing paths on your tagging server." That path must begin with a forward slash - for example, /mypath - and serves as the new public-facing address for the GTM script.
The result is that gtm.js or gtag.js loads from a URL like example.com/JBrWEDQ7LKU0c7g2 rather than from www.googletagmanager.com or from a path that exposes the container ID in plain form. A screenshot from the GTM client configuration interface, shared on LinkedIn by Paolo Bietolini, an analytics engineer focused on multi-market tracking infrastructure, shows two container IDs - GTM-12345 and GTM-6789 - each mapped to its own randomized path: /JBrWEDQ7LKU0c7g2 and /7udX respectively. The container IDs themselves are no longer exposed in any public-facing URL or script request.
"A new GTM feature (08.05) lets you serve GTM scripts from a first-party context and hide your container ID behind a randomized serving path," Bietolini wrote on May 15, 2026. "Ad blockers can't block what they can't identify, at least until they reverse-engineer the algorithm behind the random strings."
Why container IDs were a vulnerability
In the standard GTM deployment, the container ID - a string in the format GTM-XXXXXX - appears directly in the script tag embedded in the page HTML and in the request URL sent to googletagmanager.com. Ad blocker filter lists have long maintained rules targeting both the googletagmanager.com domain and patterns matching the GTM-XXXXXX format. Because container IDs are static and tied to specific accounts, blocklist maintainers can identify and target individual containers.
The first-party mode beta that Google launched in October 2024 addressed the domain portion of that vulnerability by loading scripts from the advertiser's own domain. But the container ID remained embedded in noscript fallback tags and in some request paths, leaving a residual identification point. The randomized serving path eliminates that residual exposure for the main script load. The noscript installation, according to the documentation, will continue loading the web container through first-party serving, though its dependencies may still load through first-party endpoints.
The tradeoff the documentation acknowledges is cost. Serving scripts through the tagging server "adds more load on your Tagging server and may incur a higher cost due to additional egress script requests from your server-side instance." The CDN deployment path, which the documentation explicitly labels as recommended, avoids that additional server load. The documentation also notes that additional cost due to egress requests applies only when operators choose to load scripts using the tagging server rather than a CDN.
The three-step verification process
Google's documentation specifies a verification workflow using browser developer tools. After deploying the configuration, operators open the site in a browser, navigate to developer tools, and check the Sources tab. A correct implementation shows gtm.js or gtag loaded from the domain and path specified in the client configuration - not from www.googletagmanager.com. If the Sources tab still shows googletagmanager.com as the script origin, the documentation directs operators to confirm whether the source URL was updated in the page code and whether the updated code is live.
This verification step is significant because the configuration involves two distinct code changes: the server-side client configuration in GTM, and the on-page snippet update. The snippet in the page head must replace the default googletagmanager.com script src with the tagging server URL plus the configured tag serving path. A corresponding noscript tag in the body of the page must be updated to the same base URL with the container ID appended as an id parameter.
Two implementation options for Google Ads and Floodlight
The documentation covers a specific scenario relevant to Google Ads conversion tracking: what to do with Google Ads and Floodlight tags when implementing the gateway. Two approaches are described. The first is to move those tags into the server-side container, using server-side GTM as a data staging area. According to Google, this option supports value-based bidding and allows server-side GTM to set server-side cookies. The second option keeps Google Ads and Floodlight tags in the client-side container while implementing the gateway through a CDN or load balancer to establish a first-party context for that container's script load.
The documentation includes a note that applies to both options: "Due to the dependency on third-party cookies, it's expected that some requests are still sent as third-party requests for both implementation options." This is an important constraint. The gateway addresses the script loading context and the measurement request routing, but does not eliminate all third-party cookie dependency. Marketers expecting a complete elimination of third-party data flows from this configuration will find the implementation falls short of that expectation.
HTTP response compression
One configuration detail in the updated documentation that has received little attention is the "Compress HTTP response" option in the client configuration. When enabled, the tagging server compresses supported responses - including JavaScript files. The documentation describes this as reducing data transfer from the server. For high-traffic websites where the GTM script is loaded on every page view, the bandwidth reduction from compressing the JavaScript payload could have a measurable impact on egress costs from the server-side instance.
Consent mode compatibility
The documentation directs operators to configure region-specific tag behavior as a next step after implementing the gateway, specifically for operators using consent mode. This is consistent with the regulatory context that has shaped GTM development since 2024. The German court ruling of March 2025 established that GTM cannot operate before explicit user consent under GDPR and TTDSG - a requirement that applies regardless of whether scripts load from Google's servers or from first-party infrastructure. First-party serving changes the script origin; it does not change the legal basis for processing.
Context: a year of gateway expansion
The container ID cloaking capability arrives roughly a year into the tag gateway's active expansion. Since the May 8, 2025 general availability launch with Cloudflare as the sole automated integration partner, the program has added three CDN partners. Google Cloud Platform's External Application Load Balancer integration entered beta in January 2026, and Akamai was added as the third CDN partner on January 29, 2026. Fastly launched its Ad Tag Gateway on April 8, 2026, citing a 14% signal uplift for advertisers on its network - an improvement over the 11% figure reported at the May 2025 general availability launch.
The CDN-based deployments are now supported across four major providers: Cloudflare, Google Cloud Platform, Akamai, and Fastly. Each operates on the same underlying principle - intercepting tag script requests at the CDN layer and rewriting paths to match Google's endpoints while serving the response from the advertiser's own domain. The randomized path feature described in the May 11 documentation update is most directly relevant to the tagging server path, where the GTM Web Container client configuration is the primary setup mechanism. CDN-based implementations use different configuration flows.
The broader GTM infrastructure context matters here. As documented by PPC Land in early May 2026, GTM in its current state spans six functional domains - Tag Management, Trigger and Variables, Data Layer and APIs, Security and Compliance, Testing and Debugging, and Automation and Analysis - with tag gateway representing one component within the Security and Compliance domain. The gap between how most practitioners understand GTM and what the platform now requires operationally has widened considerably since 2024.
What ad blocker operators may do next
Bietolini's observation that ad blockers "can't block what they can't identify, at least until they reverse-engineer the algorithm behind the random strings" points to a likely next step in the ongoing contest between tracking infrastructure and blocking tools. Blocklist maintainers have historically adapted to similar obfuscation techniques by identifying behavioral patterns in network requests rather than relying solely on domain or path matching. The randomized path removes one identification signal but leaves others: the JavaScript file content, the timing patterns of requests, and the network endpoints that the scripts eventually contact.
Whether filter list maintainers will develop pattern-matching rules capable of identifying randomized GTM paths without known container ID strings remains to be seen. The pace of that adaptation will determine how durable the obfuscation layer proves in practice.
Technical requirements
The full implementation for the tagging server path requires, according to Google's documentation: a server container already set up in Tag Manager, a running tagging server instance, and a configured custom server domain. Operators must open the server container, create a new client of the "Google Tag Manager: Web Container" client type, configure the allowed container IDs and the tag serving path, save and publish the workspace, and then update the on-page GTM snippet to reference the tagging server URL with the configured path. The page-level snippet modifications cover both the JavaScript snippet in the head and the noscript iframe fallback in the body.
The Web Container client type was updated alongside this documentation. According to the documentation note, "You can now serve all Google scripts (e.g. gtag.js, gtm.js) with the Web Container client." This is an expansion from earlier implementations where some dependent scripts still loaded from Google's infrastructure even after the primary script was served first-party.
Timeline
- July 2024 - Google releases First-party Mode for Google Tag Manager, an early step in first-party infrastructure development; debate begins about whether the feature bypasses ad blockers
- October 9, 2024 - Google launches First-party Mode beta for GTM with Cloudflare integration for automated setup
- May 8, 2025 - Google tag gateway for advertisers moves to general availability with Cloudflare as launch partner; 11% signal uplift reported
- January 5, 2026 - Google Cloud Platform External Application Load Balancer integration enters beta for tag gateway, adding a second automated deployment option
- January 7, 2026 - Google quietly adds data transmission controls to Google Tag settings, enabling independent management of advertising, analytics, and diagnostic data
- January 29, 2026 - Akamai added as third CDN partner for tag gateway, expanding enterprise deployment options
- April 8, 2026 - Fastly launches Ad Tag Gateway in collaboration with Google; cites 14% signal uplift for advertisers on Fastly's CDN
- May 3, 2026 - Infographic mapping GTM's full operational scope circulates widely, documenting six functional domains and the growing gap between practitioner assumptions and platform reality
- May 8, 2026 - GTM Web Container client update enables container ID cloaking via randomized serving paths, according to Bietolini's LinkedIn post
- May 11, 2026 - Google publishes updated developer documentation for Google tag gateway for advertisers formalizing the randomized serving path configuration
- May 16, 2026 - Google Tag Manager integration inside Google Ads Data Manager begins rolling out, allowing tag setup without leaving the ads platform
Summary
Who: Google, advertising technology practitioners, analytics engineers, and organizations using Google Tag Manager with server-side tagging infrastructure.
What: Google updated its tag gateway for advertisers developer documentation on May 11, 2026 to formalize a feature - noted publicly on May 8, 2026 - that allows GTM container IDs to be concealed behind randomized alphanumeric serving paths. When a new container ID is added to the Web Container client configuration in a server container, GTM automatically generates a random path to serve that container's scripts, replacing the previously static and identifiable container ID reference in public-facing URLs.
When: The GTM feature update was dated May 8, 2026 by analytics engineer Paolo Bietolini, who posted about it on LinkedIn on May 15, 2026. The formal developer documentation update was published on May 11, 2026.
Where: The configuration takes place inside Google Tag Manager's server container interface, under the Clients section, using the Google Tag Manager: Web Container client type. The resulting script is served from the operator's own tagging server domain with a randomized path appended.
Why: Ad blocker filter lists have historically targeted both the googletagmanager.com domain and known GTM container ID patterns. The randomized path removes the container ID as a blocking signal by replacing a static, identifiable string with a randomly generated path that changes per container. The feature extends the first-party serving architecture that Google has been building since mid-2024, which routes measurement traffic through advertiser-owned infrastructure to reduce the impact of browser privacy protections and ad blocker blocklists on conversion signal collection.











Discussion