Cloudflare yesterday released its inaugural 2026 Threat Report, a comprehensive analysis of the cyber threat landscape compiled by the company's in-house intelligence unit, Cloudforce One. Published on March 3, 2026, the report identifies a structural shift in attacker behavior: sophisticated, expensive intrusion techniques are giving way to high-throughput exploitation of trusted infrastructure, stolen credentials, and AI-generated content. The document draws on trillions of network signals observed across Cloudflare's global network.
The report introduces a central analytical framework called the Measure of Effectiveness, or MOE - a metric that, according to Cloudforce One, modern adversaries use to calculate the ratio of effort to operational outcome. The premise is straightforward but carries significant implications for defenders. Why spend resources on a zero-day exploit when a stolen session token achieves the same access at a fraction of the cost? Why build custom malicious infrastructure when a reputable cloud service provides free, nearly untraceable cover?
"In 2026, the most dangerous threat actors aren't the ones with the most advanced code," the report states, "it's the ones who can integrate intelligence and technology into a single, continuous system that achieves their mission in the shortest time possible."
Eight trends shaping the threat landscape
The report organizes its findings around eight key trends, each understood through the lens of MOE.
AI-powered attacker operations top the list. Cloudforce One found that generative AI is being used by threat actors for real-time network mapping, exploit development, and deepfake creation. The practical consequence is that low-skill operators can now conduct high-impact campaigns. The barrier to entry has not merely lowered - it has, according to the report, effectively vanished in several attack categories.
State-sponsored pre-positioning is the second major trend. Chinese threat actors, specifically groups identified as Salt Typhoon and Linen Typhoon, are actively targeting North American telecommunications, commercial, government, and IT services. The goal, according to Cloudforce One, is not immediate disruption but long-term geopolitical leverage - anchoring presence now to exploit it later.
Over-privileged SaaS integrations represent a third, structurally distinct risk. The report points to the GRUB1 breach of Salesloft as a case study. A single compromised API cascaded into a breach affecting hundreds of distinct corporate environments, illustrating how the connective tissue of third-party integrations can transform a localized failure into a widespread incident.
The fourth trend - weaponized trusted cloud tooling - is one the report examines in particular depth. Rather than using known malicious servers, attackers are routing their command-and-control traffic through legitimate services: Google Drive, Microsoft Teams, Amazon S3, Google Calendar, Dropbox, and GitHub. This technique, known as "living off the land" (or, in the report's terminology, "living off anything-as-a-service"), makes malicious activity nearly indistinguishable from normal enterprise traffic. Amazon SES and SendGrid, platforms designed for bulk email delivery, are also being exploited to launch phishing and malware distribution campaigns.
North Korean deepfake operatives form the fifth trend. According to Cloudforce One, North Korea has operationalized a scheme in which state-sponsored actors use deepfakes and fraudulent identities to embed themselves within Western company payrolls, conducting espionage and generating illicit revenue directly from within targeted organizations.
Token theft bypassing MFA is trend six, and the statistics here are stark. By deploying infostealers such as LummaC2 to harvest active session tokens, attackers can bypass traditional multi-factor authentication entirely - moving straight to post-authentication actions without ever triggering login alerts. The report notes that in the past three months, 63% of all logins involved credentials already compromised elsewhere, and 94% of all login attempts now originate from bots.
Phishing-as-a-service relay exploitation is the seventh trend. Mail servers, according to the report, fail to re-verify a sender's identity in certain relay configurations, a blind spot that phishing bots exploit to deliver high-trust brand impersonations directly to user inboxes. Cloudforce One's email telemetry found that nearly 46% of analyzed emails failed DMARC - an email authentication protocol - revealing a large and rapidly exploited surface area.
The eighth and final trend covers hyper-volumetric DDoS attacks. Cloudflare's telemetry established a 31.4 Tbps baseline for DDoS traffic, fueled in part by massive botnets such as Aisuru. These attacks are described as "breaking records on a regular basis," closing the window for human response and demanding automated defensive systems. Earlier Cloudflare data from 2025 showed DDoS attacks more than doubling that year, with hyper-volumetric incidents growing 700% - context that makes the new 31.4 Tbps baseline figure less surprising but no less consequential.
Threat actor groups and their techniques
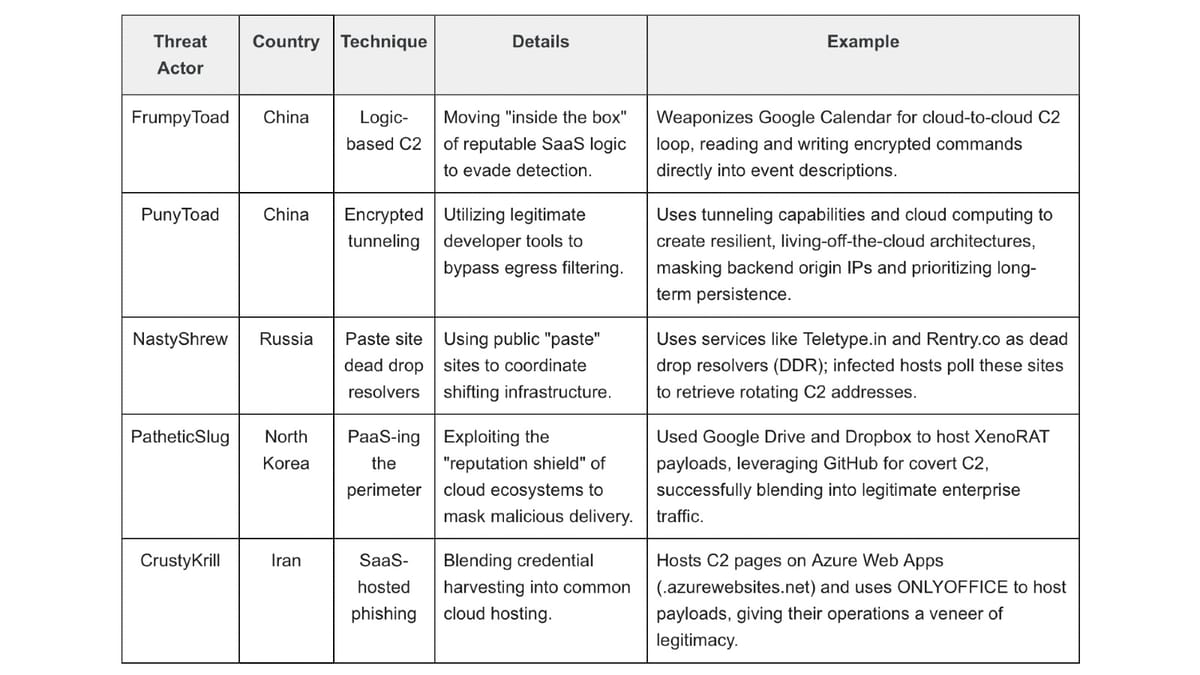
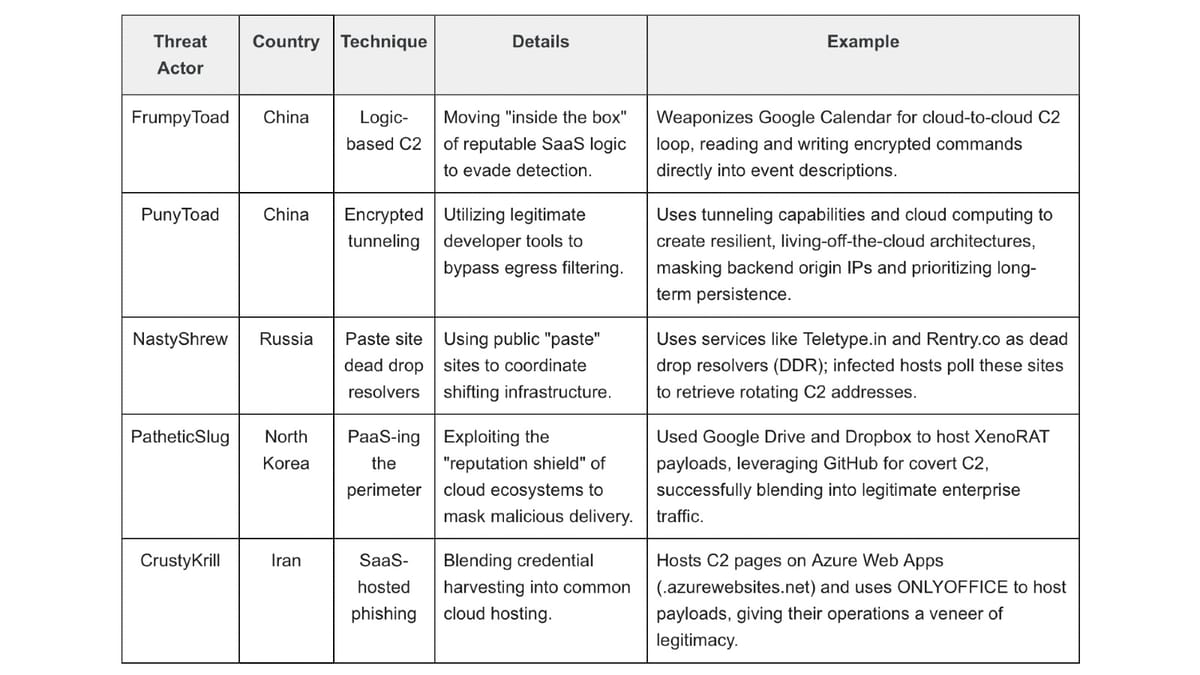
The report names five distinct groups applying these cloud-based tactics, detailing their country of origin and specific methodologies.
FrumpyToad, attributed to China, uses what Cloudforce One calls "logic-based C2" - reading and writing encrypted commands directly into Google Calendar event descriptions, operating entirely within the legitimate logic of a widely trusted SaaS application. PunyToad, also attributed to China, uses encrypted tunneling via legitimate developer tools to create resilient living-off-the-cloud architectures, masking backend origin IPs and prioritizing long-term persistence.
NastyShrew, a Russian-attributed group, uses public "paste" sites - specifically services like Teletype.in and Rentry.co - as dead drop resolvers. Infected hosts poll these public platforms to retrieve rotating command-and-control addresses, making infrastructure takedowns significantly more difficult.
PatheticSlug, attributed to North Korea, used Google Drive and Dropbox to host XenoRAT payloads, while leveraging GitHub for covert command-and-control. The report notes the group successfully blended into legitimate enterprise traffic. CrustyKrill, attributed to Iran, hosts command-and-control pages on Azure Web Apps and uses ONLYOFFICE to host payloads - extending the veneer of legitimacy to credential harvesting operations.
The pattern across all five groups is consistent: use platforms that defenders trust, avoid custom infrastructure that generates detectable signatures, and exploit the reputational shield that major cloud providers offer.
Methodology: AI dogfooding and telemetry at scale
The report's findings rest on a research methodology that Cloudforce One describes as combining global telemetry with frontline threat intelligence. Several specific investigative approaches are detailed.
In one instance, Cloudforce One tasked an AI coding agent with a self-vulnerability analysis - using the agent to uncover its own security gaps. This "dogfooding" approach uncovered CVE-2026-22813, scored 9.4 on the CVSS scale, a critical flaw in markdown rendering pipelines that allows for unauthenticated Remote Code Execution. The disclosure illustrates both the productivity gains AI agents can offer security teams and the new attack surfaces they simultaneously introduce.
The phishing-as-a-service research revealed a disappearing barrier to entry. Analysts observed attackers leveraging high-reputation domains - Google Drive, Azure, and others - to bypass conventional filters. The 46% DMARC failure rate in analyzed email traffic underscores how large a gap exists between the email security protocols that exist and the extent to which they are actually enforced.
The path forward: autonomous defense
Cloudforce One argues that the shift toward machine-speed attacks makes human-centric defense "no longer a viable shield." The report calls for a move toward autonomous defense - real-time visibility combined with automated response capabilities, designed to operate faster than the attacker even when no human operator is monitoring the situation.
Alongside the report, Cloudflare today also announced a major upgrade to its threat events platform, described as evolving from simple data access to "a fully automated, visual command center" for security operations centers.
What this means for marketing and advertising technology
The trends documented in the 2026 Cloudflare Threat Report carry direct implications for the marketing technology sector, where complex SaaS integration stacks are the norm and advertising platforms depend on trusted cloud infrastructure.
The over-privileged SaaS integration risk is particularly relevant. Marketing technology ecosystems routinely connect dozens of platforms through APIs - customer data platforms, advertising networks, analytics tools, CRMs, and more. A single compromised API credential in such a stack could, as the GRUB1/Salesloft example illustrates, cascade through hundreds of connected environments. The surge in AI-powered fraudulent mobile applications reported by DoubleVerify in September 2025 demonstrated that advertising infrastructure is already an active target for this class of attack - and the 2026 Cloudflare report suggests the underlying techniques are becoming more accessible, not less.
The deepfake operatives trend is similarly significant for organizations hiring remotely. Marketing and advertising agencies - many of which expanded remote hiring significantly - are among the most plausible targets for the North Korean scheme the report describes.
The DMARC failure rate has direct brand safety consequences. Cloudflare's own research on phishing and email securityhas previously shown how compromised email infrastructure affects enterprise operations. With nearly half of analyzed emails failing DMARC, brand impersonation at scale - including impersonation of advertising platforms and marketing software vendors - remains a viable and low-cost attack vector.
The weaponized cloud tooling trend also complicates the work of ad fraud detection. Malicious activity routed through Google Drive, Dropbox, or GitHub produces network signatures that are functionally identical to legitimate enterprise traffic, making conventional IP-reputation filtering insufficient. DoubleVerify's findings on AI-powered fraud and Cloudflare's broader infrastructure intelligence point to the same structural problem: the trust signals that defenders rely on are precisely the ones attackers are exploiting.
Cloudflare's network position - handling significant portions of global internet traffic - gives its threat intelligence a breadth that few organizations can match independently. The 31.4 Tbps DDoS baseline, the 94% bot-originated login statistic, and the 63% compromised credential rate are not projections or survey estimates. They are measurements drawn from actual traffic flowing through infrastructure that serves a substantial fraction of the internet.
For marketing professionals managing paid campaigns, the bot-originated login statistic deserves particular attention. If 94% of login attempts across the internet originate from bots, the credential stuffing risk to advertising accounts - where unauthorized access can drain budgets in hours - is not theoretical. It is an active and ongoing exposure.
Timeline
- October 2, 2024 - Cloudflare defends against a record 3.8 Tbps DDoS attack, the largest publicly disclosed at the time
- September 23, 2024 - Cloudflare launches AI Audit tools, giving publishers analytics on AI bot activity and one-click blocking
- October 27, 2025 - Cloudflare launches comprehensive TLD tracking on Radar, adding DNS magnitude metrics for 1,400+ domains
- December 20, 2025 - Cloudflare's 2025 Year in Review documents DDoS attacks peaking at 31 Tbps, 19% internet traffic growth, and AI bots accounting for 4.2% of HTML requests
- January 8, 2026 - AGCOM fines Cloudflare €14.2 million for refusing to comply with DNS-level piracy blocking orders in Italy
- March 3, 2026 - Cloudflare publishes the inaugural 2026 Cloudflare Threat Report, introducing the MOE framework and identifying eight key threat trends including AI-powered attacker operations, state-sponsored pre-positioning, and token theft bypassing MFA
Summary
Who: Cloudforce One, Cloudflare's in-house threat intelligence unit, is the author of the report. The findings concern a broad range of threat actors including Chinese state-affiliated groups (Salt Typhoon, Linen Typhoon, FrumpyToad, PunyToad), North Korean operatives (PatheticSlug), Russian actors (NastyShrew), and Iranian groups (CrustyKrill), as well as the organizations and infrastructure they target.
What: The inaugural 2026 Cloudflare Threat Report, published March 3, 2026, identifies eight major threat trends defined by a new attacker framework called Measure of Effectiveness (MOE). Key findings include: 94% of login attempts originate from bots; 63% of all logins involve already-compromised credentials; 46% of analyzed emails fail DMARC; and hyper-volumetric DDoS attacks have established a 31.4 Tbps baseline. The report also documents the widespread exploitation of legitimate cloud platforms - Google Drive, Dropbox, GitHub, Google Calendar, Microsoft Teams, Amazon S3 - as command-and-control infrastructure.
When: The report was published on March 3, 2026, drawing on intelligence gathered over the preceding year. The CVE-2026-22813 vulnerability disclosed in the report carries a 2026 identifier. The DDoS telemetry covers a three-month window preceding publication.
Where: The threats described operate globally, with particular focus on North American telecommunications and government infrastructure as targets of Chinese state actors. The cloud platforms being weaponized - Google Drive, Azure, GitHub, Dropbox - are globally distributed, making geographic containment of these techniques impractical.
Why: The report matters because it documents a structural shift in attacker strategy - away from technically sophisticated, expensive intrusion methods and toward high-throughput exploitation of the same trusted platforms that enterprises rely on daily. For the marketing and advertising technology sector specifically, the implications span credential security for advertising accounts, API integration risk across martech stacks, email authentication gaps that enable brand impersonation, and the growing use of AI to power fraud operations at scale.

