A Spanish digital advertising agency published this week a technical write-up demonstrating that Google AdsIP exclusion lists - one of the few native controls advertisers have to block fraudulent traffic sources - can be rendered ineffective through a two-IP attack method the firm calls IP Exclusion Bypass via Link Harvesting. The findings, first shared on LinkedIn by Marcos Ferreiro Rodriguez of Faktica Analytics and detailed in a full technical post on faktica.com, are grounded in a proof-of-concept the company ran against its own Google Ads account in March 2026.
The implications reach well beyond a single agency's experiment. If confirmed at scale, the technique would undermine a mechanism that advertisers have relied upon for years, and it exposes a structural gap not only in Google's own defences but in the entire ecosystem of third-party click fraud tools that use IP blocking as their primary detection layer.
What the technique does
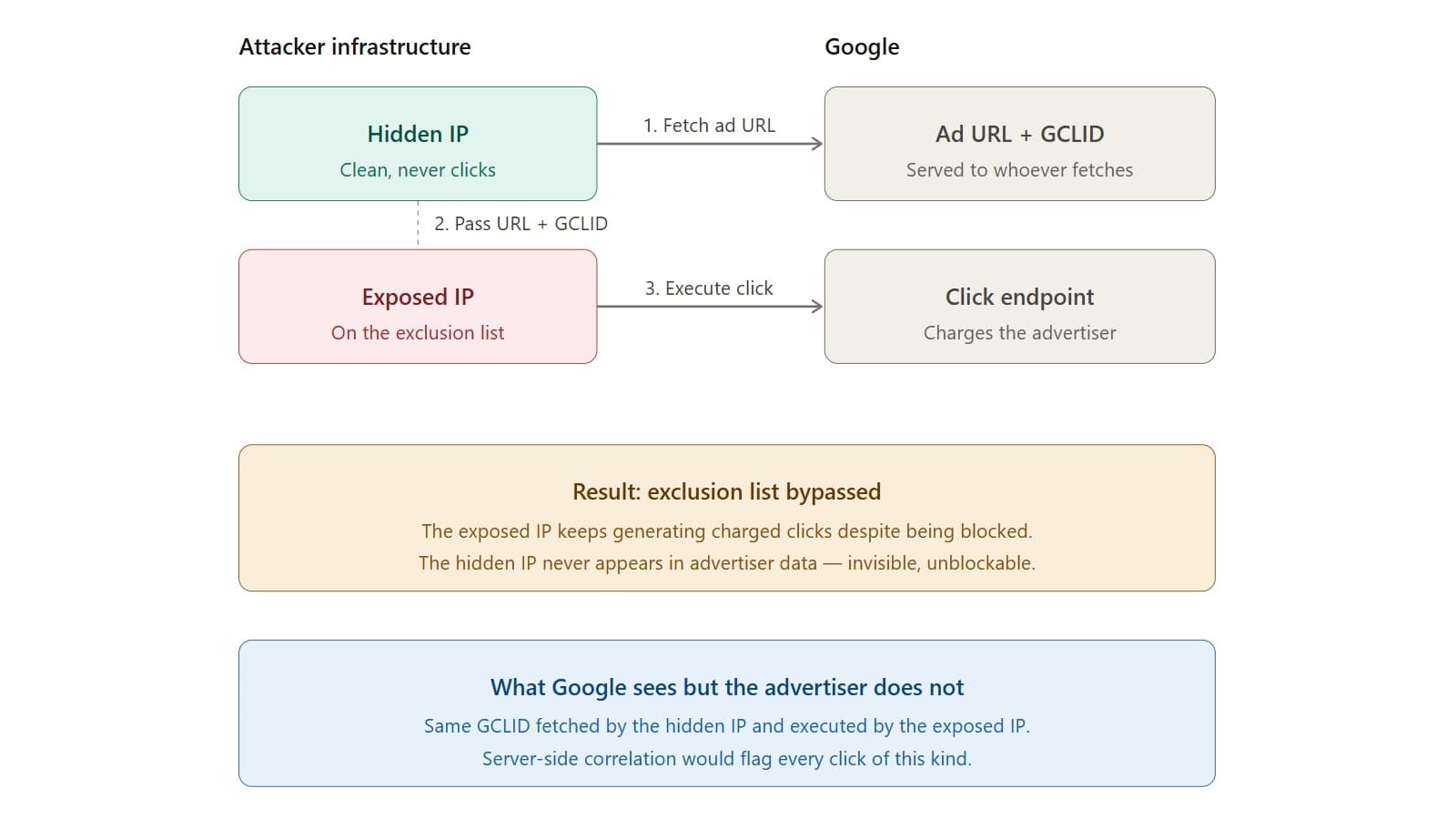
The attack separates the act of harvesting an ad URL from the act of clicking it, assigning each role to a different IP address. According to the Faktica write-up published on April 21, 2026, the setup works as follows.
A first IP - the exposed IP - has already been identified by the advertiser and added to the Google Ads exclusion list. It is visible, flagged, and in theory blocked. A second IP, which Faktica calls the hidden IP, is clean: it has never clicked on anything and never appears in any advertiser's traffic data.
The hidden IP fetches the ad URL, which in Google Ads is not a direct link to the advertiser's landing page but a Google redirect. That redirect carries the GCLID - the Google Click Identifier, a unique parameter appended to each ad click that Google uses to attribute conversions and charge advertisers. The hidden IP captures both the redirect URL and the GCLID, then passes them to the exposed IP. The exposed IP then executes the click. Google charges it.
The net result, according to the Faktica report, is that "the exclusion list becomes ineffective." The exposed IP keeps producing charged clicks despite being blocked. The hidden IP remains invisible to the advertiser because it never clicks, never registers in traffic logs, and cannot be detected or excluded. According to the write-up, it "can keep harvesting indefinitely."
What makes this structurally significant is that the hidden IP is doing the operationally meaningful work - capturing the validated, live ad URL - while the excluded IP handles only the final execution. The exclusion check, which Google applies based on the clicking IP, is therefore interrogating the wrong signal.
The proof-of-concept in March 2026
Faktica ran the attack in a controlled environment on its own Google Ads account. The company simulated an attacker targeting its own campaigns, successfully generating charged clicks from an IP that was on its exclusion list. The firm states the experiment is "internally documented and fully reproducible."
The write-up distinguishes this from theoretical analysis. Faktica has been conducting ongoing forensic work on client accounts and states it is "already documenting two fingerprints consistent with this technique being actively exploited." The first fingerprint is excluded IPs that continue producing charged clicks: the firm has documented single IPs accumulating thousands of clicks over nearly two years, with tens of clicks per day, alongside what it describes as "coordinated botnets of IPs cycling through the same set of user-agents, day after day." When advertisers add those IPs to exclusion lists, according to the write-up, Google sometimes invalidates subsequent clicks from those IPs but charges for others. An excluded IP that keeps producing charged clicks is, by definition, bypassing the exclusion mechanism.
The second fingerprint is GCLID replay patterns - single ad URLs, each carrying a unique GCLID, appearing in request logs from multiple distinct IPs, often across different countries, within short timeframes. That is precisely the trace the harvest-and-replay technique leaves: one URL captured, then executed from multiple machines. Faktica also notes this pattern provides a plausible explanation for the same GCLID being charged more than once, a billing anomaly the firm has covered separately.
Why IP exclusions were already limited
It is worth understanding how much weight IP exclusion was ever designed to carry. As PPC Land has covered previously, IP exclusion lists allow marketers to block specific IP addresses or network ranges from seeing their ads. They function as a basic targeting filter, not a security mechanism. Faktica's own prior writing acknowledges that dynamic IPs and carrier-grade NAT (CG-NAT) already erode their effectiveness, and that the firm recommends IP exclusion only "as a last resort" even in normal circumstances.
What the April 21 report adds is qualitatively different: a technique that does not just erode IP exclusions through legitimate infrastructure limitations but bypasses them entirely through deliberate separation of harvesting from clicking. The distinction matters because advertisers and third-party tools that use IP blocking as a first or primary line of defence are exposed not to accidental leakage but to purposeful evasion.
The structural implication, as Faktica describes it, is that every third-party anti-fraud tool built on top of IP blocking "inherits the same limitation." Whatever such a tool blocks at the IP layer can be circumvented with the same two-IP split. This is a significant claim for a market where IP-based blocking forms the technical core of multiple commercial fraud-prevention products.
PPC Land's overview of click fraud notes that major ad serving platforms employ multi-layered systems to detect and filter invalid traffic, operating through both pre-bid and post-serve filtration. The Faktica finding raises the question of whether post-serve filtration is catching replayed GCLIDs, given that the replayed click originates from a known, excluded IP.
The role of the GCLID in this attack
Understanding the GCLID is central to understanding why this attack is possible. When a user clicks a Google ad, the destination URL is not loaded directly. Instead, Google routes the request through a server-side redirect that records the click, assigns a unique GCLID, and then forwards the user to the advertiser's landing page. The GCLID ties the click event to a specific campaign, ad group, keyword, and device, and it is the identifier Google uses when billing the advertiser.
PPC Land has covered the GCLID in the context of auto-tagging, where Google automatically appends it to ad URLs for conversion tracking. In normal operation it is a measurement tool. In the context Faktica describes, its predictability - the fact that fetching the ad URL generates a GCLID that is then valid for a subsequent click - is the property that makes the attack work.
The hidden IP fetches the ad URL and obtains a live GCLID. That GCLID is then used by the exposed IP to execute a click Google will charge. Because the GCLID was legitimately generated at the time of harvesting, it passes server-side validation. The fraud is not in the identifier itself but in the separation between the IP that generated it and the IP that consumed it.
Google's position and what it could do
Faktica is direct about where the fix must come from. The company describes Google as being "in a unique position to close this," because Google sees both sides of the transaction that advertisers cannot. Specifically, Google records the IP that fetched the ad URL (generating the GCLID) and the IP that later executed the click - and both requests share the same click ID. That is a server-side correlation Google already possesses.
According to the Faktica report, two remediation paths are available to Google without requiring any new data collection. First, Google could flag or invalidate any click where the GCLID was harvested from a different IP than the one executing the click. Second, Google could treat clicks from IPs on an advertiser's own exclusion list as invalid regardless of which IP originally fetched the URL - removing the loophole entirely.
The firm states it has reported this issue to Google on multiple occasions, on behalf of clients "suffering substantial six- and seven-figure losses from attacks that show this exact fingerprint." As of the publication date of April 21, 2026, according to Faktica, "nothing we can observe from the advertiser side has changed, and the technique continues to work."
Google had not publicly responded to the research at the time of publication.
An unpatched problem since 2013
Faktica contextualises its finding within a longer history. In 2013, Prof. Manuel Blazquez of the Universidad Complutense de Madrid documented a structurally related vulnerability in Google AdSense. That exploit operated on the publisher side rather than the advertiser side, but shared the same architectural principle: extracting a validated ad URL through one channel and executing the click from another, exploiting Google's position as the only party with visibility into both.
According to Faktica, Blazquez reported the vulnerability to Google in 2013 and, receiving no substantive response, published his findings. The Faktica report positions the 2026 findings as "a variant of the same structural problem, still unpatched" more than a decade later.
The parallel is notable not because it proves inaction on Google's part - the AdSense context is meaningfully different from Google Ads - but because it establishes that the underlying architectural property (Google seeing both the fetch and the click while advertisers see only the click) has been known to be exploitable for over thirteen years.
The forensic evidence on client accounts
Beyond the controlled proof-of-concept, Faktica's report is notable for documenting active exploitation indicators on real client accounts. The firm describes these as consistent with - though not definitively proven to be - the harvest-and-replay technique.
The first category involves IPs generating thousands of charged clicks over periods approaching two years, with daily click volumes, patterns consistent with automated fraud, and coordination across botnets using rotating user-agents. When those IPs are added to exclusion lists, charges do not stop. They continue. According to Faktica, "an excluded IP that keeps producing charged clicks is, by definition, bypassing the exclusion mechanism."
The second category involves single GCLIDs appearing in server logs from multiple distinct IPs - sometimes in different countries - within short timeframes. This GCLID reuse pattern is the direct trace the technique leaves: one capture, multiple executions. It also explains, Faktica argues, previously documented cases of a single GCLID being billed more than once.
These clients are carrying six- and seven-figure losses. The firm has escalated cases to Google with "server-side log extracts showing clicks from excluded IPs, and GCLIDs appearing from multiple IPs." As of publication, the firm reports no resolution.
Implications for the broader market
Several dimensions of this finding matter for the programmatic advertising and search marketing community.
First, the attack is not technically complex. It requires two IP addresses with distinct roles and the ability to pass a URL and GCLID between them. The barrier to exploitation is low. Second, it is invisible to the advertiser. The hidden IP never appears in traffic data, analytics, or the Google Ads interface. Detection from the advertiser side is structurally impossible without server-side data that only Google holds.
Third, and perhaps most consequentially for the industry, the finding challenges the operating premise of a class of commercial anti-fraud tools. Products that detect and block fraudulent IPs are, according to Faktica's analysis, inheriting the same bypass: block the exposed IP, the hidden IP keeps harvesting, and the exposed IP keeps clicking. The fraud resumes immediately after any IP-level block is applied.
This does not mean IP-based anti-fraud tools have no value. Botnet detection, behavioural analysis, and post-click conversion monitoring operate on different signals and are not affected by this specific bypass. But the specific claim that IP blocking can prevent charged clicks from a flagged IP is, if Faktica's finding holds, false.
Google in 2024 reported blocking or removing 5.5 billion bad ads and suspending 12.7 million fraudulent advertiser accounts, with the company stating it uses machine learning and large language models to improve ad safety enforcement. The Faktica report does not dispute Google's general anti-fraud capabilities but argues that this specific mechanism - GCLID harvesting followed by replay from an excluded IP - falls outside what current server-side filtering catches.
The full technical write-up, including two server-log checks that advertisers can run against their own data, was published at faktica.com on April 21, 2026.
Timeline
- 2013 - Prof. Manuel Blazquez (Universidad Complutense de Madrid) documents a structurally related vulnerability in Google AdSense, reports it to Google, and publishes after receiving no substantive response.
- July 2021 - Google Ads Editor v1.1 introduces IP exclusion management, allowing advertisers to add, update, and copy IP exclusions directly in the editor for the first time.
- April 30, 2024 - Google Ads introduces IP address exclusions in Performance Max campaigns, extending the exclusion mechanism to a campaign type that previously lacked it.
- March 2026 - Faktica Analytics reproduces the IP Exclusion Bypass via Link Harvesting technique end-to-end on its own Google Ads account, generating charged clicks from an IP already on its exclusion list.
- April 21, 2026 - Faktica publishes the full technical write-up at faktica.com, detailing the mechanism, the proof-of-concept results, two active exploitation fingerprints on client accounts, and two server-log checks advertisers can run.
- April 24, 2026 - Marcos Ferreiro Rodriguez shares the findings on LinkedIn, where the post receives reactions and a repost within hours of publication.
Summary
Who: Faktica Analytics SL, a Madrid-based PPC agency selected by Google in the top 3% of Spanish PPC agencies in 2025, led by Marcos Ferreiro Rodriguez.
What: The firm published a proof-of-concept demonstrating that Google Ads IP exclusion lists - a native advertiser control for blocking fraudulent click sources - can be bypassed using a two-IP technique called IP Exclusion Bypass via Link Harvesting. A hidden IP fetches the ad URL and GCLID, hands both to an exposed IP on the advertiser's exclusion list, which then executes the click Google charges. The hidden IP never appears in advertiser-visible data. The firm also documented two active exploitation fingerprints on client accounts with six- and seven-figure losses, and reported the issue to Google with no observable resolution.
When: The proof-of-concept was conducted in March 2026. The full technical report was published on April 21, 2026. The LinkedIn disclosure appeared on April 24, 2026.
Where: The research was conducted on Faktica's own Google Ads account and documented across client accounts. Faktica is headquartered in Madrid, Spain, with offices also listed in St. Louis, Missouri.
Why: The publication follows multiple reports to Google on behalf of affected clients with no observable remediation. Faktica states the technique continues to work as of publication, and that the underlying structural vulnerability - Google holding visibility into both the harvesting and clicking IP while advertisers see only one side - has been publicly documented since at least 2013 without a server-side fix being deployed.









Discussion