AppNexus published the whitepaper The Brand Safety Risk Behind Viral Content where elaborates that "viral content goes hand-in-hand with online advertising fraud."
Viral Content (Fake News, hate speech, etc) surged on the web after the massification of Facebook, with an algorithm, often criticized to favor click-bait content.
Viral Content publishers "use the psychological triggers of shareable content to quickly generate audiences that would take a more traditional publisher years to build," says AppNexus in the Whitepaper.
What AppNexus "is seeing is that viral content publishers frequently acquire traffic from third-party sources of questionable repute. In some instances, they knowingly create or purchase fraudulent traffic with the express intent of ripping off advertisers. In others, they purchase massive audiences from vendors at below-market rates, without investigating how their partners deliver so much traffic for so little money."
And the common sense says: "the less you pay for traffic, the riskier a vendor you’ll be working with and the less likely it is that you’re getting actual humans to your site."
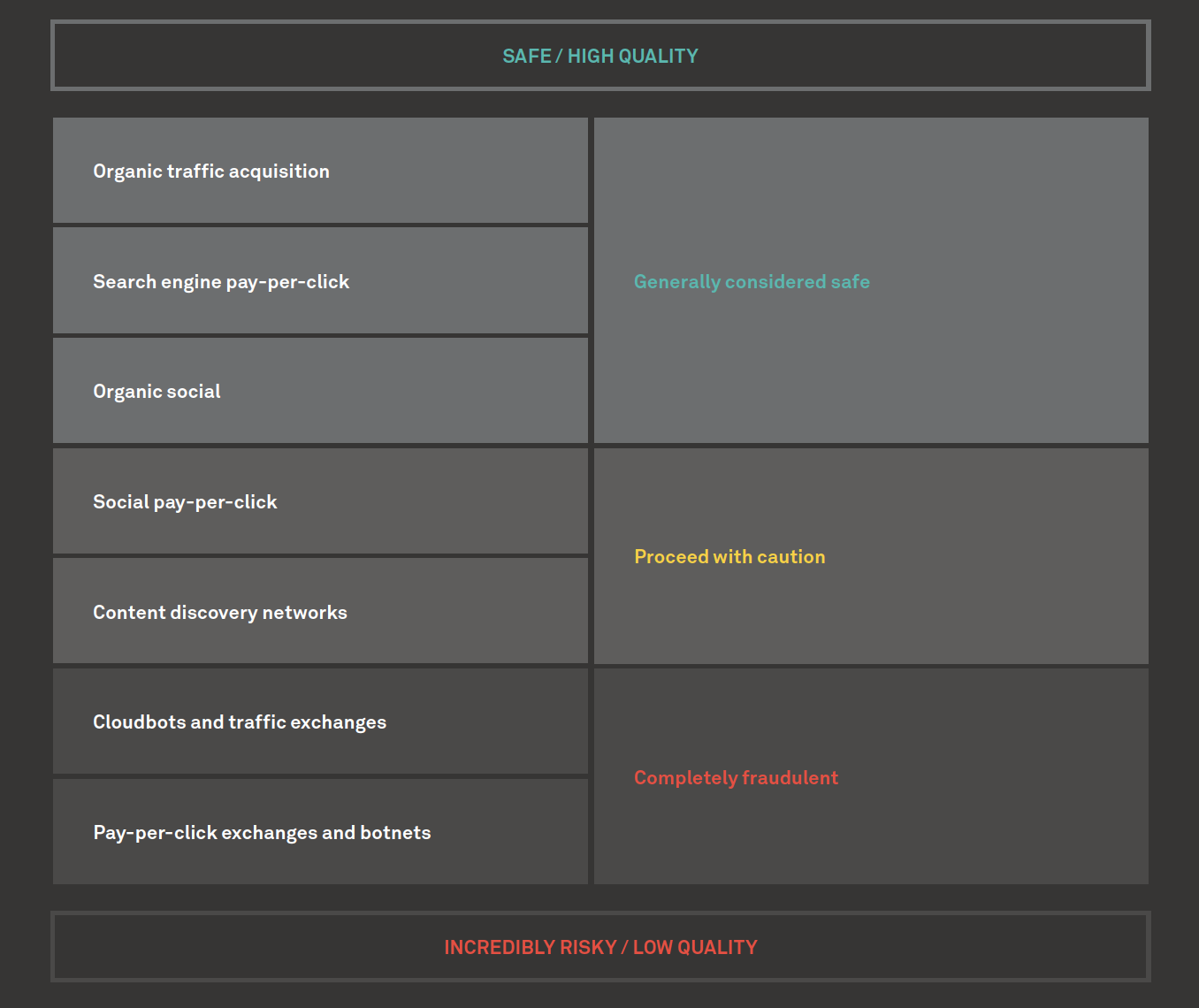
Viral Content publishers can go with the easier way and on Direct traffic; Organic search traffic or Email marketing traffic, the safest origins of traffic. Instead, they can use cloudbots and traffic exchanges or pay-per-click exchanges and botnets.
Here is the high-quality traffic sources and the low-quality traffic sources that a publisher might be using, more or less:
Methods of Ad Fraud
Browser or device hijacking programs: malware that takes over a user’s browser and navigates to specified websites without the user’s knowledge.
Bot networks: server-based browsers that masquerade as human users — in recent years, this tactic for generating non-human traffic has become more widely-used than the browser hijacking malware described above.
Ad-stuffing: a tactic in which the publisher fills a web page with invisible ads the user can’t see.
What Appnexus is doing to fight the Ad Fraud
Cluster analysis: a foundational data analysis technique that involves grouping data points together based on key similarities. Cluster analyses help us find suspicious commonalities between impressions generated by shady traffic sources.
Covisitation: a method of identifying overlaps in traffic between different websites, which helps us establish links between sites getting questionable traffic from the same sources. This study from researchers at NYU and Dstillery (formerly Media6Degrees) offers a more in-depth explanation of how covisitation can uncover instances of ad fraud.
Honeypots: a method by which we draw bots into the open by creating a fake site and then sending traffic to it from suspicious vendors. We can then analyze for signs of non-human visitors.

